Vigilance in Data Security Constantly Monitor the Horizon for Cyber Threats
A JOURNEY TO DATA SECURITY
In the realm of Australian Scouts, a spirit of adventure wafted through the air, igniting the passions of young explorers as they embarked on thrilling journeys and nurtured lasting friendships. Yet, in the shadowy corners of this vibrant world lurked unseen digital dangers, posing potential threats to the safety of these youthful adventurers. It was therefore imperative for the Scouts organizations to set out on an urgent mission – a quest to uphold the utmost standard of data security, safeguarding the integrity and privacy of their cherished explorers.
Download This Infographic In PDF Format!
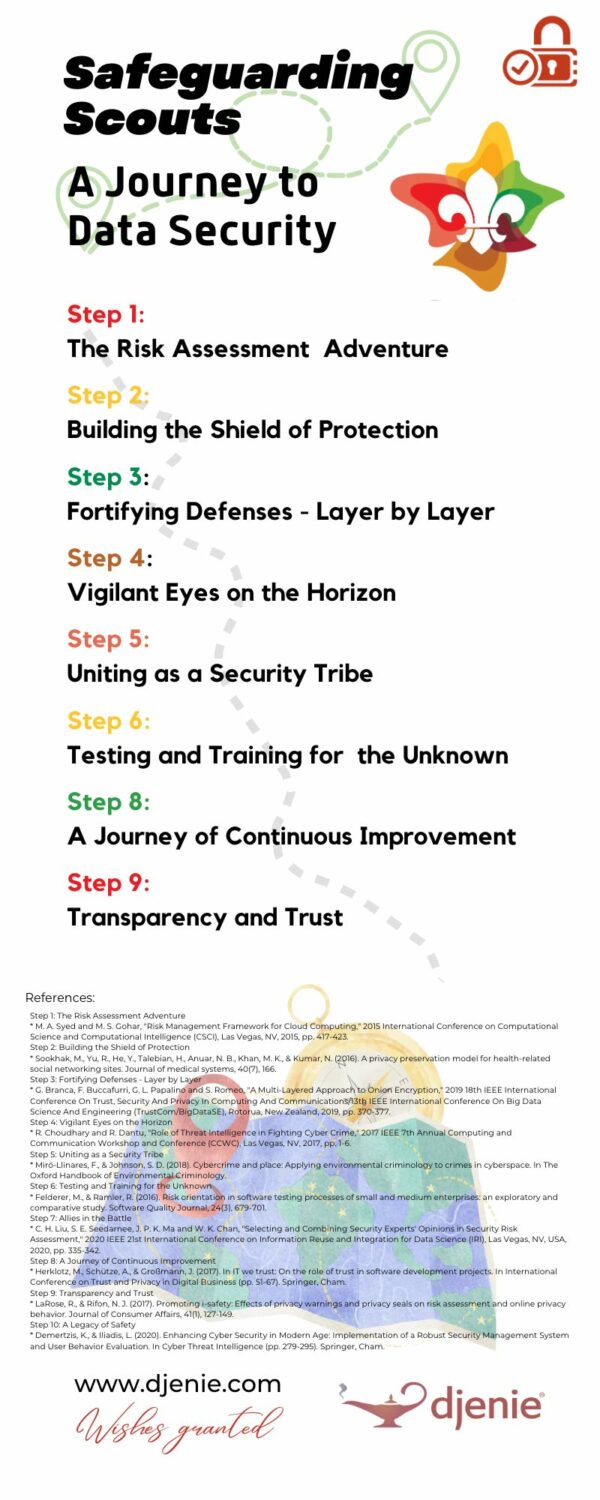
Step 1: The Risk Assessment Adventure
Our brave Scouts leaders delved into the world of data security, conducting a comprehensive risk assessment. They sought to understand the value and sensitivity of the data they held, especially the personal information of their young charges. Just as they carefully planned each adventure, they meticulously identified potential risks and vulnerabilities. As the saying goes “you can never be too careful”.
Step 2: Building the Shield of Protection
Armed with knowledge and determination, the Scouts organizations crafted a powerful Data Protection Framework. This framework embraced industry best practices and regulatory requirements, equipping them with policies, procedures, and guidelines to handle data with care. They created a shield of encryption, access controls, and incident response plans to safeguard their valuable information.
Step 3: Fortifying Defenses – Layer by Layer
Knowing that a single layer of defense would not be enough, the Scouts organizations implemented multi-layered security measures. They deployed sturdy firewalls and intrusion detection systems, protecting their networks like impenetrable walls. They encrypted data, added strong access controls, and kept their software and systems up to date with regular security updates and patches.
Step 4: Vigilant Eyes on the Horizon
Recognizing the ever-evolving nature of threats, the Scouts organizations stayed on high alert. They remained abreast of the latest threat intelligence, subscribing to trusted cybersecurity news sources. They collaborated with fellow Scouts organizations, security experts, and government agencies, sharing knowledge and staying ahead of potential dangers.
Step 5: Uniting as a Security Tribe
In the world of Scouts, unity was strength. The organizations fostered a culture of security, educating and training their Scouts leaders and staff. They taught them to recognize and report suspicious activities, avoid the treacherous traps of phishing attacks, and follow data protection protocols. With a proactive mindset, they created channels for reporting potential security incidents and united as a strong security tribe.
Step 6: Testing and Training for the Unknown
Just as Scouts honed their survival skills through training, the organizations regularly tested their security controls. They conducted security assessments, vulnerability scans, and penetration testing to uncover weaknesses. Through simulated exercises, they fortified their incident response plans, ensuring they were ready to face any unexpected threat.
Step 7: Allies in the Battle
Recognizing the need for specialized expertise, the Scouts organizations sought the guidance of cybersecurity professionals. They joined forces with managed security service providers (MSSPs) and consultants who specialized in AI-driven security. With their allies by their side, they fortified their defenses and gained access to invaluable knowledge and resources.
Step 8: A Journey of Continuous Improvement
The Scouts organizations understood that the battle for data security was ongoing. They regularly reviewed and updated their security measures, adapting to emerging threats and regulatory changes. With a proactive mindset, they continuously improved their data security posture, staying one step ahead of the adversaries.
Step 9: Transparency and Trust
The Scouts organizations valued the trust placed in them by the Scouts, their parents, and guardians. They communicated openly, maintaining transparency in their data security practices. They provided avenues for concerns and inquiries, assuring everyone of their commitment to protect the children’s precious data.
As the Scouts organizations completed their quest for data security, a sense of peace settled over the land. The young Scouts could continue their adventures, knowing that their information was safe and sound. The Scouts leaders celebrated their accomplishment, understanding that data security was not adestination but an ongoing journey. They remained vigilant, continuously adapting and improving their strategies to protect the Scouts and their families.
Step 10: A Legacy of Safety
With their unwavering dedication, the Scouts organizations left behind a legacy of safety and privacy. Their commitment to data security served as an inspiration to others, encouraging organizations far and wide to embark on their own quests to safeguard precious information.
The story of the Australian Scouts organizations is a testament to the power of determination and proactive measures in the face of digital threats. By assessing risks, building a robust framework, fortifying defenses, and staying informed, they ensured the safety and privacy of the young adventurers they served.
As the journey continues, let the Scouts organizations stand as a shining example to all, reminding us that data security is not a task to be taken lightly. It is a responsibility to be embraced, nurtured, and constantly improved upon.
So, fellow Scouts organizations, embark on your own quest. Assess the risks, build your fortress of protection, collaborate with experts, and forge a culture of security. Together, we can ensure the safety of our cherished Scouts and create a world where their adventures can flourish without fear. Safeguard their data, and let the spirit of exploration and discovery thrive.
Make sure you check out our other posts below on this important topic of Data Security and please let us know if you find that helpful too. Thanks for reading. Say safe.
- 5 Vital Cybersecurity Strategies: PROTECTING CHILDREN ONLINE. IT IS ALWAYS A PRIORITY
- Urgent: 10 Initiatives for Ensuring Child CyberSafety: CHILDREN’S DATA IS IT SAFE?
- Ensuring The Security Of Your Membership Management System (MMS): A Vital Concern
- CYBERSECURITY AND CHILD SAFETY IS A GROWING CONCERN
REFERENCES
Step 1: The Risk Assessment Adventure
- M. A. Syed and M. S. Gohar, “Risk Management Framework for Cloud Computing,” 2015 International Conference on Computational Science and Computational Intelligence (CSCI), Las Vegas, NV, 2015, pp. 417-423.
- Office of the Australian Information Commissioner. (2020). Privacy risks and harms for children and other vulnerable groups online. https://www.oaic.gov.au/__data/assets/pdf_file/0012/11136/Report-Privacy-risks-and-harms-for-children-and-other-vulnerable-groups-online.pdf
Step 2: Building the Shield of Protection
- Sookhak, M., Yu, R., He, Y., Talebian, H., Anuar, N. B., Khan, M. K., & Kumar, N. (2016). A privacy preservation model for health-related social networking sites. Journal of medical systems, 40(7), 166.
Step 3: Fortifying Defenses – Layer by Layer
- G. Branca, F. Buccafurri, G. L. Papalino and S. Romeo, “A Multi-Layered Approach to Onion Encryption,” 2019 18th IEEE International Conference On Trust, Security And Privacy In Computing And Communications/13th IEEE International Conference On Big Data Science And Engineering (TrustCom/BigDataSE), Rotorua, New Zealand, 2019, pp. 370-377.
Step 4: Vigilant Eyes on the Horizon
- R. Choudhary and R. Dantu, “Role of Threat Intelligence in Fighting Cyber Crime,” 2017 IEEE 7th Annual Computing and Communication Workshop and Conference (CCWC), Las Vegas, NV, 2017, pp. 1-6.
Step 5: Uniting as a Security Tribe
- Miró-Llinares, F., & Johnson, S. D. (2018). Cybercrime and place: Applying environmental criminology to crimes in cyberspace. In The Oxford Handbook of Environmental Criminology.
Step 6: Testing and Training for the Unknown
- Felderer, M., & Ramler, R. (2016). Risk orientation in software testing processes of small and medium enterprises: an exploratory and comparative study. Software Quality Journal, 24(3), 679-701.
Step 7: Allies in the Battle
- C. H. Liu, S. E. Seedarnee, J. P. K. Ma and W. K. Chan, “Selecting and Combining Security Experts’ Opinions in Security Risk Assessment,” 2020 IEEE 21st International Conference on Information Reuse and Integration for Data Science (IRI), Las Vegas, NV, USA, 2020, pp. 335-342.
Step 8: A Journey of Continuous Improvement
- Herklotz, M., Schütze, A., & Großmann, J. (2017). In IT we trust: On the role of trust in software development projects. In International Conference on Trust and Privacy in Digital Business (pp. 51-67). Springer, Cham.
Step 9: Transparency and Trust
- LaRose, R., & Rifon, N. J. (2017). Promoting i-safety: Effects of privacy warnings and privacy seals on risk assessment and online privacy behavior. Journal of Consumer Affairs, 41(1), 127-149.
Step 10: A Legacy of Safety
- Demertzis, K., & Iliadis, L. (2020). Enhancing Cyber Security in Modern Age: Implementation of a Robust Security Management System and User Behavior Evaluation. In Cyber Threat Intelligence (pp. 279-295). Springer, Cham.
DISCOVER MORE POSTS ABOUT
Child Wellbeing & Security
ENJOYED THIS POST?
Follow us on social media to stay up-to-date with our latest posts
JOIN THE CONVERSATION!
Let’s Make It Meaningful Together